🎣 Monitoring the Situation
Plus: autonomous trucking just raised $113M, California is fighting to keep 20,000 drivers, Arrive's 2026 truckload freight forecast, and more.
Hackers posted 19,000 fake loads under TLS’s name. Here’s how it happened and what brokers need to know.

On March 10, 2025, Transportation and Logistical Services, Inc. (TLS) had what seemed like just another Monday. That was until their phones started ringing off the hook. Confused carriers were calling about loads that TLS had never posted.
Hackers had taken over a TLS DAT account and flooded the load board with 19,000 fraudulent loads—causing mass chaos for both TLS and the carriers who unknowingly fell into the scam.
Here’s how it happened—and how brokers and carriers can protect themselves.

It all started with a phishing email.
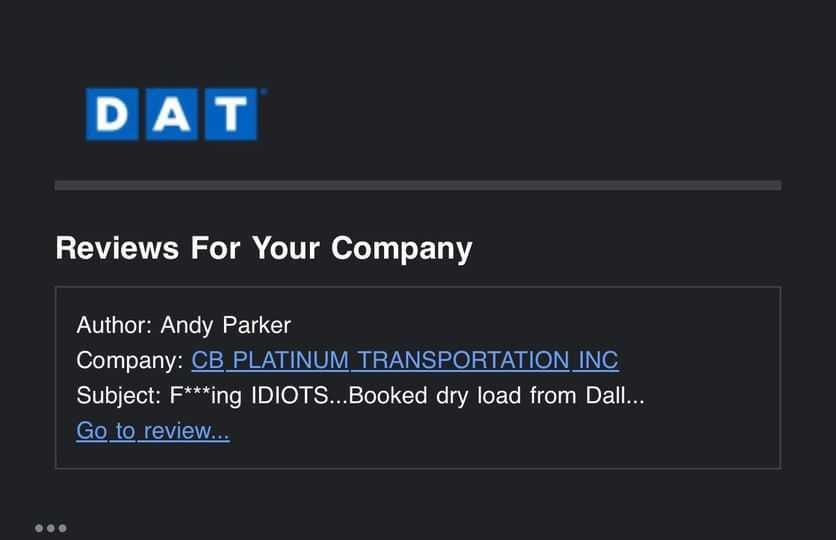
An employee at TLS received an email that looked like it came from DAT, urging them to log in immediately.
The email contained a fake DAT login link, and once the employee entered their credentials, the hackers had everything they needed.
🔹 They stole the employee’s DAT and email login credentials.
🔹 They logged into the DAT account from an IP address in New York.
🔹 They had full control—and TLS had no idea yet.
“We’ve notified our employees to be more careful about what they click on when receiving possible phishing emails.” – Jennifer Nolan, Logistics Coordinator, TLS
We’ve covered these DAT phishing attempts before, and it’s critical to train your entire team to spot and avoid them.

Now in control of TLS’s account, the scammers moved fast, flooding DAT with 19,000 fraudulent load postings—all under TLS’s name.
“Carriers were asking us for information about loads they saw posted that we had no idea about.” – Jennifer Nolan
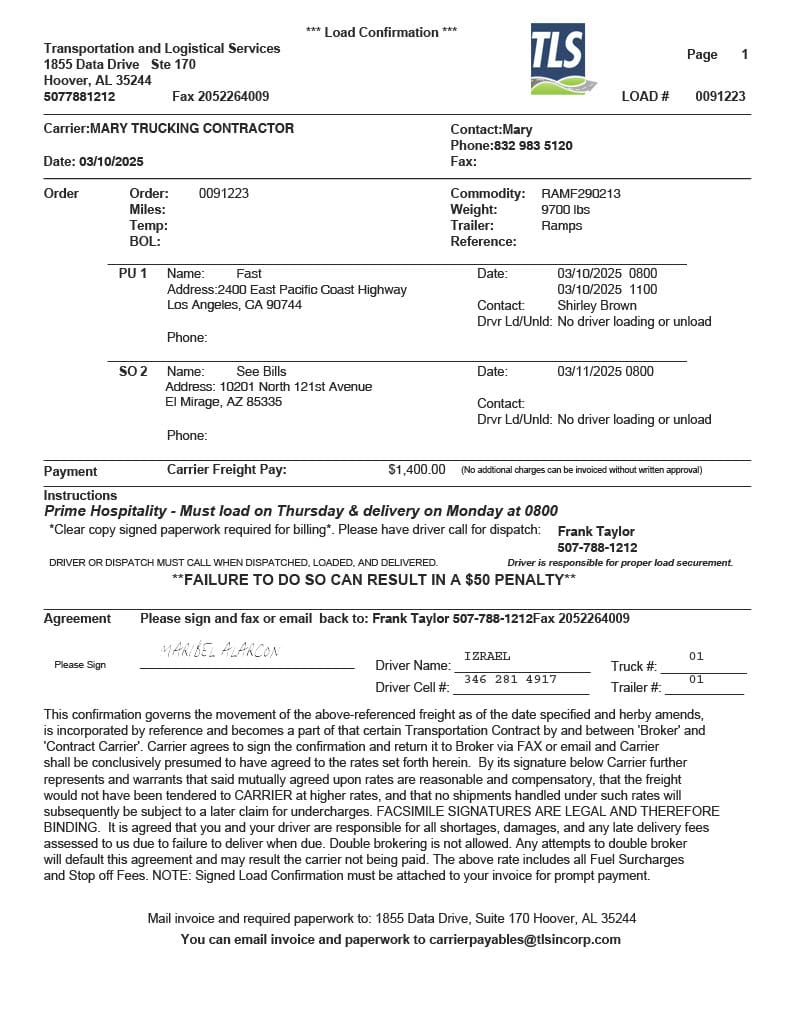
Scammers knew that just posting fake loads wouldn’t be enough—so they backed them up with convincing paperwork.
“The rate confirmations they sent to carriers had different fonts and alignment because they altered one of ours from 2022.” – Jennifer Nolan
Managing freight claims across emails, spreadsheets, and carrier portals is a mess. FreightClaims.com brings it all into one centralized system. Track, manage, and resolve claims efficiently from a single platform.
By 8:15 AM, TLS’s Birmingham and Dallas offices were under siege—not from hackers, but from thousands of phone calls from confused carriers.
“We received so many calls, it shut down our phone system.” – Jennifer Nolan
Once TLS realized what was happening, they immediately contacted DAT for help. DAT acted fast, shutting down the compromised account and restricting admin access.
“DAT’s response was great. They acted very quickly to help us disable the jeopardized account.” – Jennifer Nolan
At least two carriers had already picked up and delivered loads, thinking they were working with TLS.
Another carrier requested a Truck Order Not Used when they realized something was off.
“We know of at least two carriers that picked up and delivered loads.” – Jennifer Nolan

Epay Manager is giving away a brand new Scotty Cameron putter at the TIA Capital Ideas Conference in San Antonio!
After securing their account, TLS took action to prevent this from happening again and to warn others.
“We posted a notification on our Facebook page and our website, so if anyone who was a victim of the fraudulent activity searched for us, they would know we were also a victim.” – Jennifer Nolan
We recently interviewed Aleksander Frelas, Founding Member of Velite.io, a cybersecurity company. He discussed the importance of corporate cybersecurity and tips on preventing hacks.
For Brokers:
1. Train employees to recognize phishing scams—these attacks start with one wrong click.
2. Enable multi-factor authentication (MFA) for DAT and other key platforms.
3. Regularly monitor load postings to catch suspicious activity early.
For Carriers:
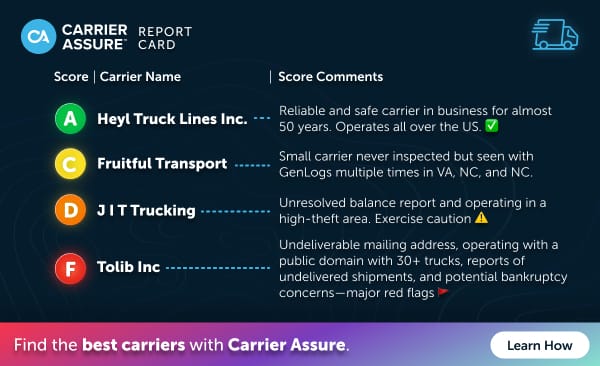
1. Always verify loads with the broker before committing.
2. Scrutinize rate confirmations—inconsistencies in fonts, alignment, or missing details can be red flags.
3. If the broker stops answering calls after booking a load, it’s a scam.
“If it seems too good to be true, it probably is.” – Jennifer Nolan
TLS took the right steps once they discovered the breach, and DAT responded quickly—but this attack raises bigger questions.
Why was a single hacked account allowed to post 19,000 loads in such a short time?
Should load boards have automated fraud detection for abnormal activity?
As cargo theft and fraud continue to rise, the entire industry needs stronger defenses to prevent attacks like this before they happen.

FREIGHT HUMOR
Join over 14K+ subscribers to get the latest freight news and entertainment directly in your inbox for free. Subscribe & be sure to check your inbox to confirm (and your spam folder just in case).